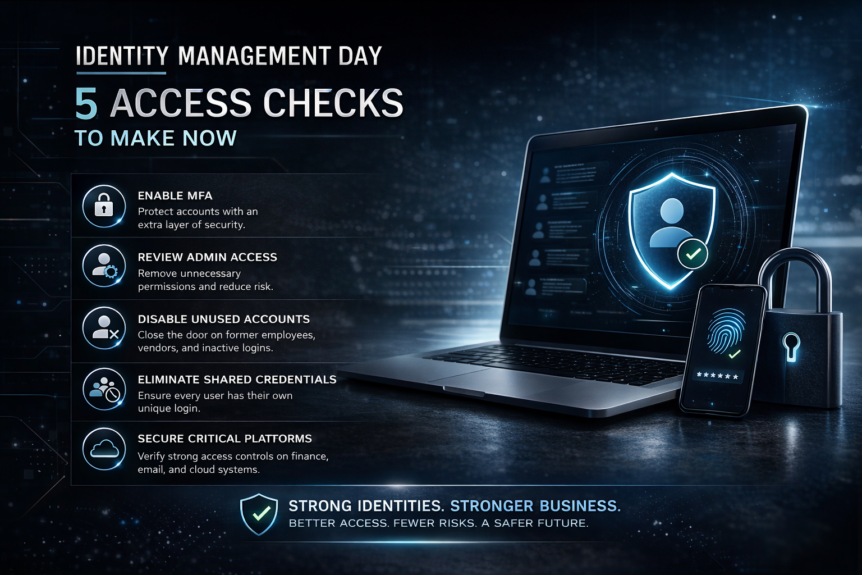
April 14, 2026 is Identity Management Day, an annual awareness campaign focused on helping organizations better understand how digital identities are secured and how access should be managed across the business. The official 2026 theme is centered on the reality that identity is no longer only about employees logging into laptops and email. It now includes human identities, machine identities, …
Why VOIP Can Make or Break a Chiropractic Practice
If you run a chiropractic practice in Maryland or the DMV, your phone system isn’t just a utility, it’s your revenue engine. Every new patient starts with a call. And if your phone system drops calls, routes incorrectly, lacks reporting, or can’t scale with growth, you are quietly losing revenue every week. That’s why modern chiropractic practices are switching to …
Legal Industry Cloud Security Trends: Client Data in the Cloud
Law firms and the broader legal industry are rapidly adopting cloud platforms for document management, collaboration, and remote work, but security must evolve alongside convenience. Recent Legal Industry Cyberattacks: What Firms Should Know In 2025, law firms continued to be prime targets for sophisticated cybercrime, with multiple high-profile incidents showing why cloud security and proactive IT management are essential. Recent …
Data Protection in Healthcare – Youth Data
How Engler IT Protects Youth Health Data Healthcare organizations that serve youth carry an added responsibility: protecting highly sensitive data while navigating complex consent and privacy requirements. Engler IT partners with healthcare providers to ensure youth health records are secure, compliant, and accessible only to authorized users. The First Major Step Healthcare Organizations Should Take Separate Youth Health Data from General …
Comcast Hit With $1.5M Fine For Cyber Breach
Originally posted on Bleeping Computer: Comcast will pay a $1.5 million fine to settle a Federal Communications Commission investigation into a February 2024 vendor data breach that exposed the personal information of nearly 275,000 customers. The breach occurred in February 2024, when attackers hacked into the systems of Financial Business and Consumer Solutions (FBCS), a debt collector Comcast had stopped …
Achieving FERPA Compliance
FERPA (Family Educational Rights and Privacy Act) protects student education records and governs how schools collect, store, and share student information. From an IT perspective, schools must demonstrate that systems, policies, and procedures keep student data secure and private. Achieving FERPA Compliance – here are the key milestones: 1. Assess Current Systems & Data Inventory Goal: Full visibility into data and risk …
CMMC Compliance for Engineering Firms
Engineering firms working with the Department of Defense (DoD) or federal subcontractors must comply with the Cybersecurity Maturity Model Certification (CMMC). This ensures that Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) are protected from cyber threats. Understanding CMMC Compliance for Engineering Firms CMMC compliance depends on the level required by your contracts: For engineering firms, Level 2 is often …
What Happens During a School IT Audit?
An IT audit evaluates the security, policies, infrastructure, and practices of a school’s technology environment. For K–12 schools, charter schools, and private institutions, audits often focus on: During an audit, auditors may: Goal: Determine whether the school is adequately protecting sensitive student data and IT systems and following legal and regulatory requirements. How Engler IT Benefits Schools as Their MSP During an Audit …
CMMC Compliance – Step by Step
1. CMMC Is 70% Technical Controls — IT Is Core to Compliance Most of CMMC’s Level 1 and Level 2 requirements involve: These are IT disciplines, not legal or consulting tasks. Engler IT implements the actual technologies that meet these controls, not just paperwork. 2. Policies Alone Don’t Make You Compliant Many cybersecurity firms deliver policies in a binder and leave. …
Top 10 U.S. Cities Most at Risk for Cyberattacks
In today’s digital age, cybersecurity isn’t just a concern for tech companies. It’s a critical issue for cities across the United States. From ransomware attacks to data breaches, urban centers are increasingly becoming prime targets for cybercriminals. And yes, they can hit you while you’re down, like during a storm or unexpected outage. Understanding which cities are most at risk …
- Page 1 of 2
- 1
- 2