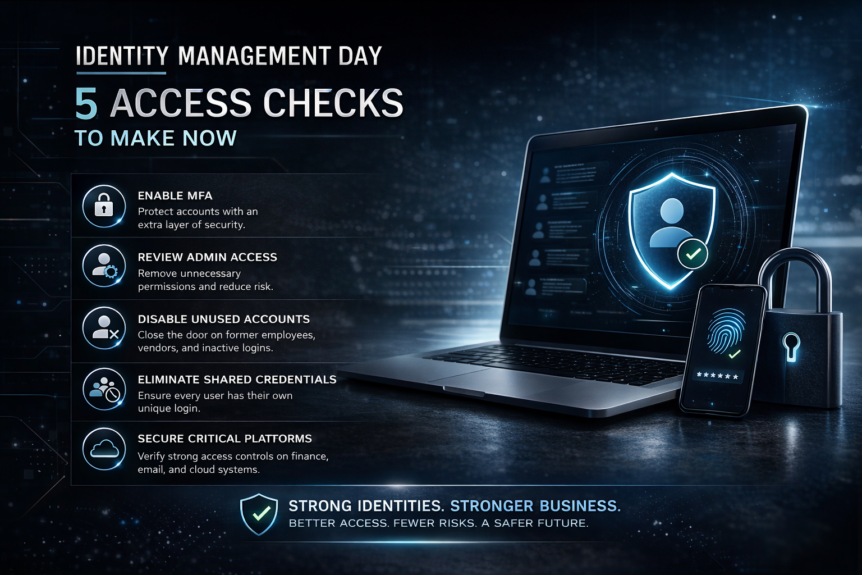
April 14, 2026 is Identity Management Day, an annual awareness campaign focused on helping organizations better understand how digital identities are secured and how access should be managed across the business. The official 2026 theme is centered on the reality that identity is no longer only about employees logging into laptops and email. It now includes human identities, machine identities, …
ATM Jackpotting – U.S. DOJ Charges 54 in ATM Jackpotting Scheme Using Ploutus Malware
originally published by Hacker News, December 2025: The U.S. Department of Justice (DoJ) this week announced the indictment of 54 individuals in connection with a multi-million dollar ATM jackpotting scheme. Ploutus Malware The large-scale conspiracy involved deploying malware named Ploutus to hack into automated teller machines (ATMs) across the U.S. and force them to dispense cash. The indicted members are …
Breach News – City of Baltimore (Again)
The City of Baltimore lost more than $1.5 million to a business email compromise (BEC) scam after a fraudster tricked employees into changing a contractor’s bank account information. Investigators just announced that in December 2024, an unspecified attacker submitted a fraudulent supplier contact form using the name of a legitimate company employee to gain access to the vendor’s Workday account. …
Achieving FERPA Compliance
FERPA (Family Educational Rights and Privacy Act) protects student education records and governs how schools collect, store, and share student information. From an IT perspective, schools must demonstrate that systems, policies, and procedures keep student data secure and private. Achieving FERPA Compliance – here are the key milestones: 1. Assess Current Systems & Data Inventory Goal: Full visibility into data and risk …
CMMC Compliance for Engineering Firms
Engineering firms working with the Department of Defense (DoD) or federal subcontractors must comply with the Cybersecurity Maturity Model Certification (CMMC). This ensures that Controlled Unclassified Information (CUI) and Federal Contract Information (FCI) are protected from cyber threats. Understanding CMMC Compliance for Engineering Firms CMMC compliance depends on the level required by your contracts: For engineering firms, Level 2 is often …
What Happens During a School IT Audit?
An IT audit evaluates the security, policies, infrastructure, and practices of a school’s technology environment. For K–12 schools, charter schools, and private institutions, audits often focus on: During an audit, auditors may: Goal: Determine whether the school is adequately protecting sensitive student data and IT systems and following legal and regulatory requirements. How Engler IT Benefits Schools as Their MSP During an Audit …
Top 10 U.S. Cities Most at Risk for Cyberattacks
In today’s digital age, cybersecurity isn’t just a concern for tech companies. It’s a critical issue for cities across the United States. From ransomware attacks to data breaches, urban centers are increasingly becoming prime targets for cybercriminals. And yes, they can hit you while you’re down, like during a storm or unexpected outage. Understanding which cities are most at risk …
MFA failure costs Hamilton $18m in cyber insurance payout
On February 25th, 2024, a sophisticated ransomware attack struck the City of Hamilton, crippling roughly 80 percent of its network. This included business licensing, property-tax processing, and transit-planning systems. Cybercriminals proceeded to demand an $18.5 million ransom that the city refused to pay. In April 2025, a new and interesting facet to this story emerged. Hamilton’s insurer denied the city’s insurance …
Why CMMC Compliance Matters for Engineering Firms
As cyber threats continue to evolve and national security becomes increasingly dependent on digital infrastructure, the DoD has taken firm steps to secure the defense industrial base (DIB). One of the most critical developments in this effort is the Cybersecurity Maturity Model Certification (CMMC) — a framework designed to protect Controlled Unclassified Information (CUI) across the supply chain. For engineering firms in Maryland, …
Why Every Federal Contractor Should Get a Dark Web Scan
Uncover Hidden Threats Before They Become Compliance and Security Nightmares In today’s hyperconnected world, cybersecurity risks no longer stop at your network’s edge. For businesses operating in the federal contracting space, the stakes are even higher. A single credential leak or compromised email address on the dark web can expose your organization to serious consequences — from data breaches to …
- Page 1 of 2
- 1
- 2