Cybersecurity is no longer just a concern for large corporations, hospitals, or government agencies. In this episode of the Cyber Brisket Podcast, Chris Engler sits down with Reginald Andre, founder and CEO of ARC Solvers, to talk about the real risks businesses face today, from cyberattacks and AI misuse to downtime, unmanaged devices, and the false sense of security that comes from …
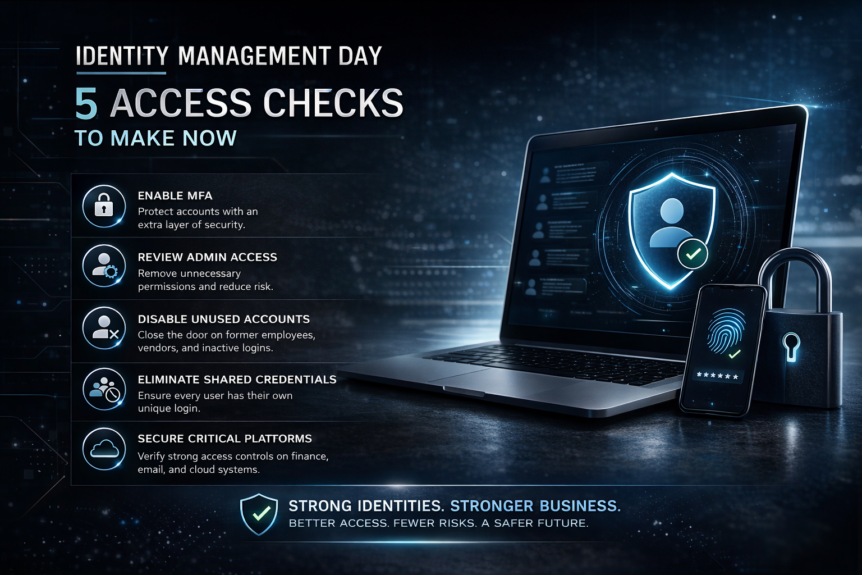
Identity Management Day + 5 Access Checks to Make Now
April 14, 2026 is Identity Management Day, an annual awareness campaign focused on helping organizations better understand how digital identities are secured and how access should be managed across the business. The official 2026 theme is centered on the reality that identity is no longer only about employees logging into laptops and email. It now includes human identities, machine identities, …
How Dentists Can Use AI To Grow Their Business
If you operate a multi-location dental clinic across the DMV and greater Maryland, you’re managing far more than patient care. You’re juggling scheduling systems, imaging software, billing workflows, cybersecurity risks, compliance requirements, and staff across multiple offices. AI is transforming how modern dental groups operate. But without the right infrastructure and managed IT support, AI becomes expensive noise. That’s where Engler …
Engler IT honored by The 20 – Leader in Managed IT Awards
US – NORTHEAST REGION WINNER Engler IT, a managed services provider based in Maryland (greater DC), is proud to announce it has been honored with the US-Northeast Regional Award at the inaugural Leader in Managed IT Awards, held during MSP SUMMIT at The 20 HQ in Plano, Texas. The Leader in Managed IT Awards debuted live at MSP SUMMIT (January …
Google Extensions Hack: 840,000+ users hit by malicious browser extensions. Uninstall these ASAP!
originally published by PC World, January 2026 Security researchers are now warning of a targeted malware campaign that involves malicious software hiding in certain browser extensions. The wave of attacks, dubbed “GhostPoster”, targets Chrome, Firefox, and Edge users. There have been over 840,000 attacks since December, and the extensions went undiscovered in the Google App Store since 2020. How the GhostPoster …
DoorDash Data Breach
DoorDash, the popular app for ordering food and groceries, disclosed a recent data breach. A social-engineering scam was the culprit. The company’s response claims that there is no indication that any fraud or identity theft have occurred. Here’s what happened: How Major Corporations Respond Disappointingly, DoorDash mentioned in their press release to affected users below that they are trying to …
Data Protection in Healthcare – Youth Data
How Engler IT Protects Youth Health Data Healthcare organizations that serve youth carry an added responsibility: protecting highly sensitive data while navigating complex consent and privacy requirements. Engler IT partners with healthcare providers to ensure youth health records are secure, compliant, and accessible only to authorized users. The First Major Step Healthcare Organizations Should Take Separate Youth Health Data from General …
Chris Engler sits as special guest on the Lights, Sprinklers, Action Podcast
This episode of Lights, Sprinklers, Action teams up with Chris Engler of Engler I.T. to talk about practical AI and automation for businesses — especially how leveraging these technologies can improve operations while still keeping data security and safety top of mind. Chris Engler gives insight on: 1. What AI Can Do for Small & Medium BusinessesChris discusses how modern AI tools and automation solutions can take over routine tasks, …
IT Risk Management for Contractors
Construction companies operate in dynamic environments, including working between multiple job trailers, field devices, subcontractor platforms, and tight project deadlines. Engler IT works with contractors to manage IT risk without slowing the job down. One Thing Contractors Should Do Now: Secure and Standardize Field Technology Field devices, including laptops, tablets, and phones used on jobsites, are one of the largest unmanaged risks for …
ATM Jackpotting – U.S. DOJ Charges 54 in ATM Jackpotting Scheme Using Ploutus Malware
originally published by Hacker News, December 2025: The U.S. Department of Justice (DoJ) this week announced the indictment of 54 individuals in connection with a multi-million dollar ATM jackpotting scheme. Ploutus Malware The large-scale conspiracy involved deploying malware named Ploutus to hack into automated teller machines (ATMs) across the U.S. and force them to dispense cash. The indicted members are …
- Page 1 of 2
- 1
- 2