April 14, 2026 is Identity Management Day, an annual awareness campaign focused on helping organizations better understand how digital identities are secured and how access should be managed across the business. The official 2026 theme is centered on the reality that identity is no longer only about employees logging into laptops and email. It now includes human identities, machine identities, and automated or agentic identities that interact with systems every day. This year’s event reflects how much the identity conversation has expanded and why access management can no longer be treated like a background IT task.
That shift matters because identity has quietly become one of the most important control points in modern security. Most businesses have spent years adding platforms, cloud tools, collaboration apps, mobile workflows, finance systems, and third-party integrations. Every one of those systems depends on some kind of identity and access model. Someone has to log in. Something has to authenticate. Some account has to be granted permission. Over time, those permissions stack up, exceptions are made, temporary fixes become permanent, and visibility gets weaker. The end result is not always immediate chaos. More often, it is slow exposure. Access becomes broader than it should be, ownership becomes unclear, and security teams are left managing risk through a patchwork of habits instead of a deliberate system. Identity Management Day exists to push that conversation back to the front where it belongs.
One of the most important ideas behind this year’s campaign is that identity risk is not limited to people. The 2026 materials place a major emphasis on machine identities and the growing role of automated access. That includes service accounts, scripts, pipelines, apps, scheduled jobs, cloud roles, and emerging AI or agent-based workflows. The identity surface inside an organization is now much larger than many leaders realize. In fact, Identity Management Day’s official 2026 messaging specifically highlights the challenge of managing human identities together with machine and agentic identities, because securing only the human side of access is no longer enough.
That is also why identity issues are often missed until they become expensive. Security leaders do not usually lose sleep over a single stale account or one overly broad admin permission. But that is exactly how access risk builds. A former employee still has access to a cloud tool. A shared login is being passed around inside a team. An admin account still exists because no one wants to break something. MFA was rolled out in some places but not all. Finance platforms and email systems were added quickly and never reviewed afterward. None of these problems feels dramatic in isolation. Together, they create the kind of gaps attackers look for and the kind of confusion that makes incident response harder than it should be. CISA’s guidance consistently emphasizes core steps like requiring MFA, reviewing user access, disabling inactive accounts, and applying least privilege because those fundamentals directly reduce the number of easy access paths available to an attacker.
If there is a good takeaway from Identity Management Day, it is this: organizations do not need to solve every identity challenge in one week. They do need to stop assuming that access is under control just because users can sign in and work gets done. Strong identity management is not about adding friction for the sake of it. It is about making sure the right people and systems have the right access for the right reasons, and that access can be adjusted, reviewed, or removed cleanly when it changes. The goal is safer operations, cleaner support, and fewer silent risks sitting in the background.
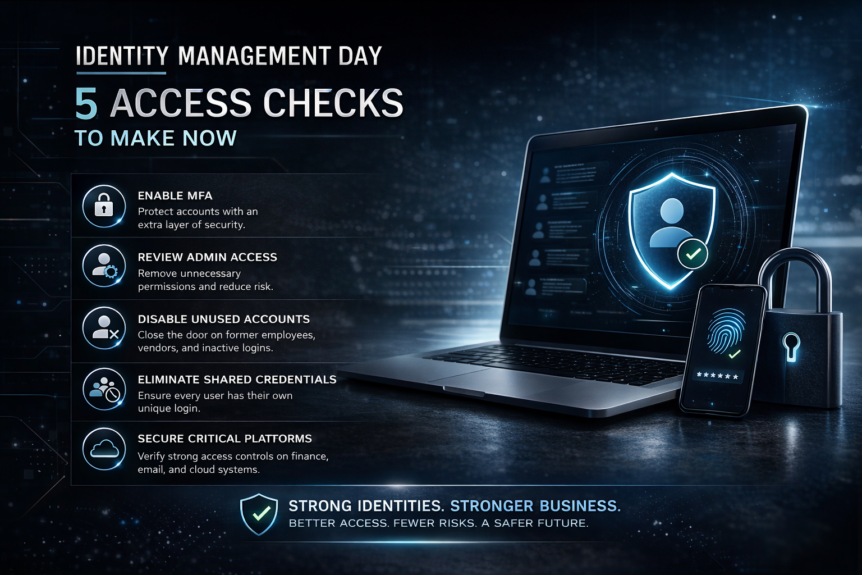
A practical place to start is with five access checks that can be done now.
1. Confirm MFA is enabled on all business-critical accounts.
CISA is direct on this point: multifactor authentication is one of the simplest and most effective ways to reduce the risk of account compromise. MFA adds another layer beyond the password, which means a stolen or guessed password alone is less likely to hand over access to an attacker. That matters most on the systems that can do the most damage if compromised, such as email, remote access tools, finance systems, admin consoles, cloud platforms, and privileged accounts. If MFA is only enabled in some places, then the organization still has uneven exposure. Identity management gets stronger when MFA is treated as a standard for critical access, not an optional setting left to individual users.
2. Review admin access and remove unnecessary permissions.
Over-permissioned accounts create avoidable risk. CISA and NIST guidance both reinforce the principle of least privilege, meaning users and accounts should have only the minimum access needed to perform their duties. That sounds simple, but many businesses drift away from it over time. Employees change roles. Contractors stay in systems longer than expected. Managers approve access “just in case.” IT teams keep elevated permissions in place to avoid interrupting workflows. The result is an environment where too many people can do too much. Reviewing admin rights is one of the fastest ways to reduce that risk. It also improves accountability, because it becomes clearer who actually owns critical actions inside the environment.
3. Disable unused accounts and former employee logins.
Dormant accounts are one of the easiest identity problems to ignore and one of the easiest to fix. CISA’s Cybersecurity Performance Goals recommend reviewing user access and disabling accounts after inactivity, ideally through an automated process. CISA has also separately advised organizations to remove access for exiting employees and disable accounts that are no longer needed. This is a basic but important lifecycle discipline. If an identity is no longer active in the business, it should not remain active in the environment. The same logic applies to unused vendor accounts, stale test accounts, and temporary accounts created during projects. Every unnecessary account is another possible path into systems that no longer has a legitimate business purpose.
4. Make sure shared credentials are not being used across teams.
Shared logins feel convenient, especially in fast-moving environments. But they weaken both security and accountability. When multiple people use the same credentials, it becomes harder to know who accessed what, when changes were made, or who is responsible for risky behavior. NIST control guidance has long recognized shared and group accounts as higher-risk account types, and official control catalogs identify shared or group accounts as the kind of account organizations may want to prohibit because of the increased risk they introduce. Shared credentials also make access reviews much weaker, because there is no clean relationship between a person and a permission set. If teams still rely on shared passwords, that is a sign the organization needs cleaner role-based access, better delegation practices, or a more secure way to manage privileged workflows.
5. Verify finance, email, and cloud platforms have proper access controls in place.
Not every system carries the same business risk. Some platforms are more sensitive because they affect money, communications, and infrastructure. Email remains a major target because it is tied to resets, approvals, executive communication, and internal trust. Finance systems carry obvious fraud and payment risks. Cloud platforms often hold the keys to core infrastructure, storage, apps, and identity integrations themselves. Reviewing access in these areas should include confirming MFA, identifying privileged roles, checking whether unnecessary users still have access, and making sure controls match the sensitivity of the platform. The point is not to create red tape. The point is to make sure the systems that matter most are not governed by outdated assumptions or inherited permissions.
The bigger lesson here is that identity management is not just a cybersecurity conversation. It is an operational one. When access is clean, support is easier. Offboarding is faster. Audits are less painful. Permission questions are easier to answer. Troubleshooting improves because ownership is clearer. Security becomes more consistent because controls are tied to actual roles and risk rather than scattered exceptions. That is why identity management should be viewed as part of the organization’s operational maturity, not just part of its compliance checklist. The best identity programs reduce noise as much as they reduce risk.
Identity Management Day is a good reason to pause and take a hard look at how access is really being managed. Not how it is supposed to work on paper. Not how it worked two years ago. How it works right now. Who has access? Why do they have it? Is it still needed? Is it protected properly? Are machine and automated identities being managed with the same seriousness as user accounts? Those questions are no longer optional in a modern business environment. The identity footprint is bigger, faster, and more complicated than it used to be, and the businesses that treat identity as a living security discipline will be in a much stronger position than the ones that keep treating it like a one-time setup task.
Strong identity management makes support cleaner, access safer, and security incidents harder to pull off. That is the real value behind this year’s message. Start with the basics. Check MFA. Tighten admin access. Remove stale accounts. Eliminate shared credentials. Recheck the systems that matter most. You do not need a massive transformation to make meaningful progress. You just need to stop letting identity drift in the background.